Ransomware. It’s a word we’re being inundated with everywhere we turn.
And rightfully so. Over the last few years, it has become more and more prevalent. And definitely a bigger concern for IT departments. Every week, it seems like we read another news story about the latest attack on an organization — sizes aren’t spared, either. Ransomware attacks are happening to offices, both big and small. No one is immune.
In the first half of 2022 alone, there were a total of 236.1 million ransomware attacks worldwide. And in a survey done by Sophos, it is estimated that there has been a 78% increase in ransomware attacks over the course of the last year. Moreover, the average cost to recover from a ransomware attack is $1.4 million. Think about that.
Everything from customer data to taxpayer information, confidential data used by your local police department, and just about any other instance you can think about. Building a single computer back to a functioning, healthy state due to a virus isn’t nearly as stressful as having to restore all of your data from a malicious attack by a bad actor, oftentimes with the looming threat of having this data held captive in their hands until you payback a specific fee.
The thought of your organization or department being crippled by a hostile takeover of your data & IT infrastructure is scary. But it doesn’t have to be.
Let’s talk about how you can protect your business or office from outside intrusions. These steps will help to ensure that you are equipped to withstand and recover from a ransomware attack on your data, should one ever take place (although, let’s hope it doesn’t).
One of the first things to begin with, is snapshotting.
What is Snapshotting?
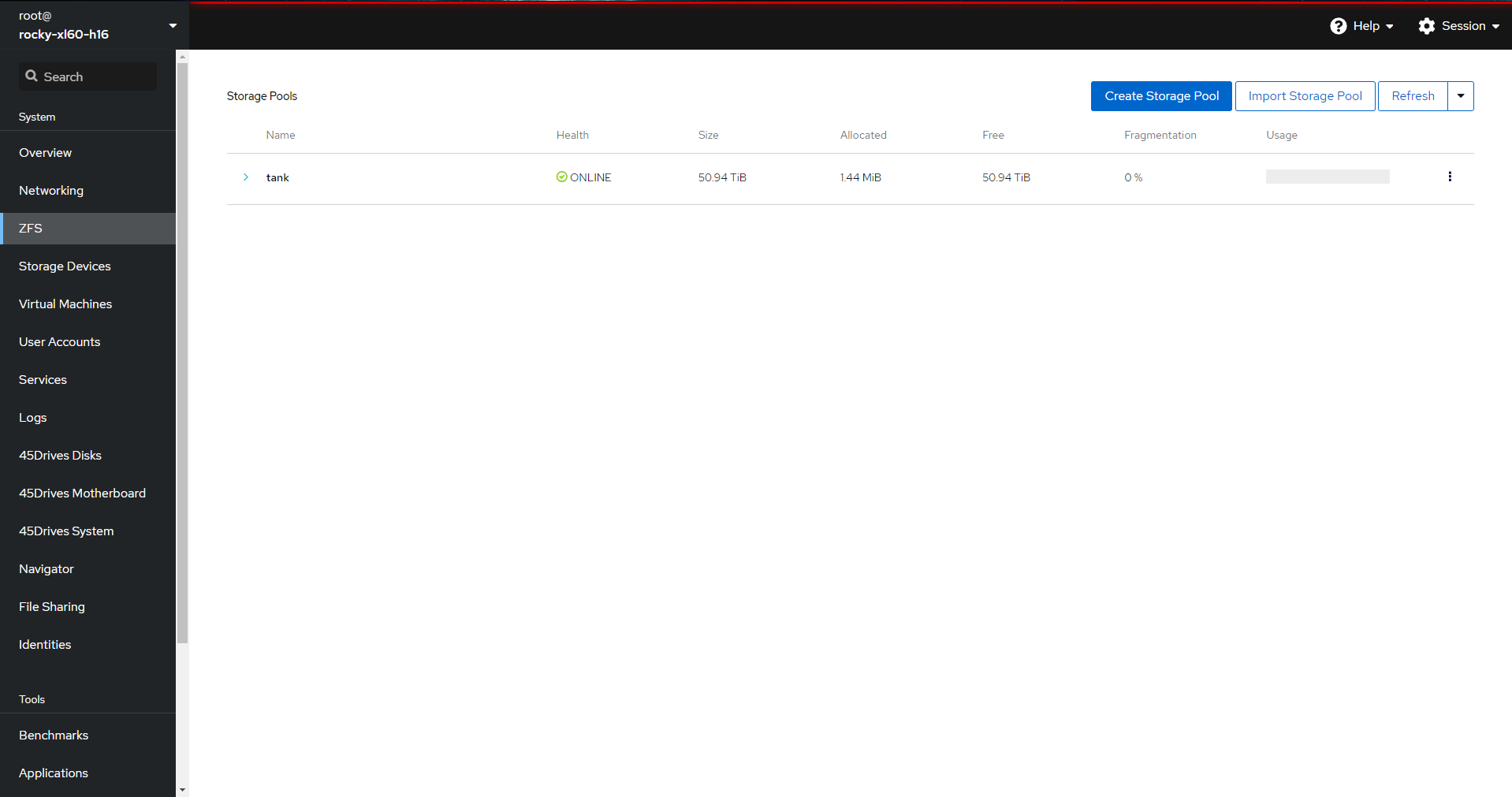
We’re really big fans of the ZFS filesystem here at 45Drives.
Throughout our blog, our YouTube Channel and our Knowledge Base, we talk about the ZFS filesystem often. As well as the many ways it can be used. But this blog is all about snapshotting to mitigate the effects of a ransomware attack.
A snapshot in ZFS, in the simplest term, is a copy of a data set or a volume set to a specific period of time, e.g. One hour, one day, one week, etc. These copies can then be rolled back upon if and when needed. Furthermore, they exist immutable, meaning they cannot be changed or modified.
Because snapshots are, in essence, immune to modifications, they act as a great protection against common forms of ransomware. Generally, when a typical ransomware attack takes effect, a workstation(s) and its files become infected & modified. This can then trickle through to other workstations in your organization, thereby rendering dozens, possibly even hundreds of pieces of infrastructure contaminated and locked.
By rolling back to these different data “points” in time taken through snapshots, you can access those specific files — or even full directory trees. This gives a great level of security against varying levels of these nefarious types of attacks.
And by leveraging our HoustonUI, one of our Storage Architects, Spencer, walks you through how to bolster your snapshot policy with a few simple steps.
Segmenting Your Snapshots
Another incredibly useful thing about snapshots is the fact that you can actually compartmentalize your data sets on a per filesystem or per data set basis.
What does this mean, exactly?
Well, if you have the resources and ability within your team to implement stringent data segmentation, e.g. Each department within your organization having its own data set, like the Finance Department, the Human Resources Department, etc. — you can implement snapshot policies that are specific to those departments.
For example, your finance department may have some of the most sensitive data within your organization. Or, it may be changing regularly. You can create more aggressive snapshot policies for these conditional circumstances, allowing you to roll back to certain data points for one department if the attack was contained – or to work quickly to contain it. This is also helpful for simple day-to-day activities, like minimizing the impact of accidental file deletion.
Using Automated ZFS Replication/Backup in Houston UI is a good place to look to get started with backups using ZFS filesystems; however, snapshots are not technologies unique to the ZFS filesystem. Similar options exist in Ceph; snapshots for both CephFS and RBD, as well as object versioning in S3.
We would be remiss, of course, if we did not say that snapshots are not a replacement for backup copies. A backup strategy beyond this implementation is critical to not just protection from ransomware but also just a smart practice to uphold in general.
A Good Backup Strategy
Establishing a regular, solid backup plan is one of the first and most important things you can do to provide the foundation for dependable ransomware protection.
We talk about the 3-2-1 Backup Method in one of our older blogs, but some of the key takeaways include:
But a reliable backup strategy is only the tip of the iceberg. This method, and this method alone, is insufficient to shield you from immunity.
You need to take that a step further by implementing snapshotting, like we just discussed, for even more protection.
What does a ransomware attack mean for your data?
Ransomware attacks are getting cleverer by the day. Not only are they more sophisticated and stealthier — their impact on an organization is becoming more disastrous.
They are all too easy to launch as well. Think about it:
Even if your staff are properly trained to detect malware-laden emails or to monitor the external links they are visiting carefully, a simple and honest mistake can mean total devastation for your office/department. An email comes through, looking like it has been sent by a colleague; in that email, a normal-looking attachment is craftily titled to look like a purchase order or an important memo.
An unsuspecting staff member opens that email, then BAM.
Ransomware slowly starts to infect their computer and their files, and then it slowly begins to creep through your network — then all of your data. Sometimes, this can even go undetected for weeks!
Scary stuff.
So, how can you keep your business safe and ensure a smooth recovery should a ransomware attack spread through your IT infrastructure?
Recover from a ransomware attack
One of the first things you can do is shrink the intervals at which your snapshots take place. Especially if you have an active filesystem, making your most precious data more susceptible to infection. For example, if you are snapshotting your data every 24 hours, you are at a greater risk of losing your file(s). By cutting that down to, say, every 5-10 minutes, your odds of a catastrophic ransomware impact are much lower.
Due to its robust and evolving profile, however, simply having good ransomware policies is not enough. Software is available to help detect ransomware of the open and closed varieties. At 45Drives, we are happy to provide recommendations for you to assist with the process of sourcing these, but beyond that?
The next, most obvious thing to do is to power down your server infrastructure. By taking these offline, your servers can no longer send or receive data — essentially locking them down to prevent further modifications or damage. In this lockdown mode, you and your team (or with the help of 45Drives) can then identify the impacted workstations, wipe them clean of the ransomware and then provision them to start up safely again.
Still not sure if your set-up is strong enough?
We can help with that. At 45Drives, we take data very seriously.
Lately, we have seen an influx of customers who are not only increasingly concerned about ransomware attacks but are also being proactive when it comes to further strengthening their systems.
That is why we created a Ransomware Plan. This plan is designed to aid in the reduction of a negative impact should your office ever fall victim to a ransomware attack. By working with you and your team to safeguard your servers, our team of specialized Data Storage Architects will make sure that you have all of the necessary tools in place to weather a ransomware attack.
We will work with you to set up the appropriate snapshotting policies, run regular “fire drill” tests on your data and, should an incident befall your organization; we will be there to help restore your systems to a healthy, functioning state again.
Interested in learning more? Contact us today to talk about your Ransomware Plan.
Newsletter Signup
Sign up to be the first to know about new blog posts and other technical resources