Your Guide to IPMI Hardening and BMC Security
Some of you may have seen the recent stories about security flaws found within the Baseboard Management controllers (BMC) within SuperMicro Motherboards. While this is indeed very serious, many of the articles were somewhat misleading by taking something that is by its very design, a very powerful feature – and giving the impression that the feature itself is the flaw. This is not the case, and the BMC is something many System Admins rely on in the enterprise daily.
The flaws that have been found are how the BMC handles authentication. If you would like to read an in-depth explanation of the flaws please refer to the original article written by the Security research firm Eclypsium right here.
Speaking in general terms, there were four flaws found which include plaintext authentication, unencrypted network traffic, weak encryption methods, and finally an authentication bypass. This sounds scarier than it is because we are committed to building secure environments here at 45Drives. We will be going over some best practices you should observe if you’re using the IPMI feature on your 45Drives product that will put your mind at ease.
So, you’re asking yourself – am I at risk? With a list of SuperMicro motherboards that are susceptible to this vulnerability, chances are your board might be on that list – but don’t worry!
We are here to help you not only become protected from this flaw but to provide you with some best practices that will harden your security from possible future attack vectors.
Vulnerable SuperMicro Motherboards:
- X9SRL
- X9SCM-F
- X10DAI-O
- X10DRL-I
- X10SAT
- X10SRI-F
- X11DPH-T
- X11DPL-I
- X11SPL-F
- X11SSH-LN4F
- A complete list can be found here
If you use your IPMI to log in to your server from within your local network and never externally then your potential for risk becomes much lower.
People who are most at risk are the ones who port forward their IPMI to the internet to manage their server from an outside location. This is NOT a good idea – no matter how good you think your password or security is. If you have your IPMI port forwarded on your router, I advise you to stop right here and remove that rule from your router before continuing. If you need to have access to your IPMI from outside of your network, we will be giving you information on how to safely do this later on in this guide.
Let’s talk about Patches
The flaws in question were found by a security researching firm called Eclypsium. SuperMicro has been aware of these issues for a few months and has been working with Eclypsium to resolve them. As a result, they have been very proactive in releasing patches for many of their motherboards. SuperMicro has already released patches for the X10 and X11 series, with the X9 series coming soon. The first step will be to update your SuperMicro BMC Firmware.
For a detailed step-by-step guide on how to update your 45Drives BMC IPMI firmware, head on over to our Knowledge Base and follow this guide.
If you’re unable to take your storage server offline right now to apply the patches but are still concerned about the possible security vulnerability, then you can disable virtual media network traffic by blocking TCP port 623 for now. Once you find a better time, you can perform the necessary security patching.
Please note: This will remove the ability to install any software through your IPMI until you can properly update your motherboard’s firmware.
To block this port, log in to your server’s IPMI. From here, move your mouse cursor over the Configuration tab, and then click on the Port option.
Once inside the Port tab, uncheck the Virtual Media Port and then click Save.
This will block any access to all Virtual Media options through IPMI until security patches can be applied.
Don’t Default
There are a few best practices of the IPMI that everyone should have in place to keep their infrastructure as safe as possible – and they are super simple!
First: Change the default username/password. To do this, log in to your IPMI. Once inside take your cursor and move it on to the Configuration tab, then click on users.
Inside of the users’ window, modify the name of the root account named ADMIN to something unique for system admins who use this interface – preferably something they will remember.
Removing anything that is “default” is always a good idea for security purposes. While modifying the root account’s name you should create a difficult password as well. From here you may also create other users who may have access to the IPMI. Be sure to grant proper privileges to any created users, and do not grant administrative privileges if the user does not require them.
Note: Instead of creating users through the IPMI, you can instead authenticate your IPMI with things like Active Directory security groups, a RADIUS server, or LDAP.
Best Network Practices
Once the IPMI user logins have been hardened and the BMC flaws have been patched, it’s time to look at some network security that is specific to the IPMI. Remember:
The worst configuration with the highest possibility of security breaches is where BMC’s through the IPMI is directly routable to the Internet through the use of port forwarding. This allows a bad actor to have a direct attack vector, where the only security separating them from your server is an IPMI login screen. This combined with security flaws like the ones talked about at the beginning of this article could allow even unsophisticated attackers to gain full access to your server.
To the security-savvy people reading this may seem like something no one would ever do, but the security firm who found this round of security flaws in the BMC also found 47,000 BMC ports exposed to the Internet. Ensure you are not one of these 47,000!
The next configuration is seen in many small business networks. This is not ideal from a best-practices security standpoint, however, is better than the previous option.
This is where the BMC IP management interfaces are running on the same internal LAN network as all the other devices on the network. The BMC cannot be accessed directly over the Internet because there is a Firewall in place between the WAN and the LAN, but the interface can be accessed through any devices on the internal network. This still runs the risk of having a user’s machine becoming compromised and may give the bad actor a direct vector of attack to what is considered critical infrastructure (the server through IPMI).
If you’re currently in this situation with your network and unable to revamp to the specifications in the third network example, there is a way to add an extra layer of protection. This is called IP Access Control. This can be found within your IPMI. Once logged in, click on the Configuration tab. From here, scroll down to IP Access Control. If you are unable to create a proper management VLAN reserved only for administration seen in the next network example, this will give you the option to only allow IPMI to be accessed by specific systems. Note: Be sure to set a static IP address on the systems you intend to use for IPMI.
First, click enable IP Access Control
Next, click Add. Once inside the Add Rule prompt, add the address and subnet mask for the system you wish to add. From here you can set the policy to either accept or reject requests from this system. This can be done for as many or as few devices as you wish.
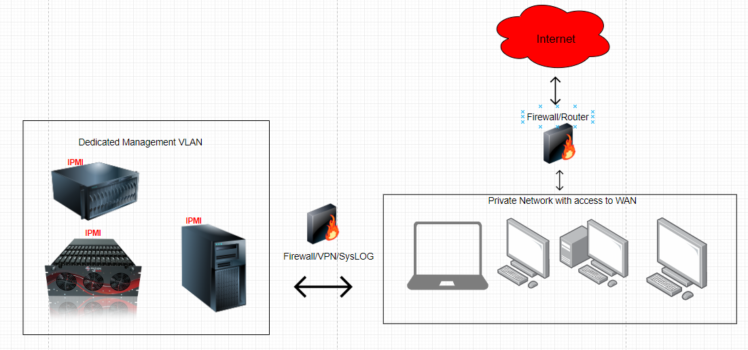
The third and final network scenario we will be discussing is the ideal solution for a network with robust, multi-layered security.
This is when you have your BMC IPMI’s for your server, located on a completely separate management VLAN with extremely limited access combined with management systems dedicated to performing the administration tasks required. From here, if IPMI access is required from a remote location outside of the network, the only way to do this would be through the use of a secure VPN. Finally, proper logging by way of a Syslog server is integral to any robust network security.
Note: IPMI has an extremely simple integration with Syslog servers. Simply log in to your IPMI, click on Configuration and then click on the Syslog tab. Check enable Syslog, and then enter the IP of your Syslog server, and the port it listens on, and click Save.
Summary:
This was a lot to take in – so let’s recap:
- A security research firm named Eclypsium found security flaws found within the BMC on SuperMicro motherboards.
- We talked about who is most at risk, followed by the motherboards 45Drives use that are vulnerable.
- We gave tips on how to patch your motherboard, as well as a Band-Aid you may be able to apply in case your server is part of critical infrastructure, and can’t be rebooted at the moment.
- We showed how to create custom user names and passwords.
- We gave an overview of some of the possible network scenarios, ranking them from the worst to the best practices, and showed some great tips on how to lock down your IPMI even without the use of network segregation.
- We touched on the use of a Syslog server and just how invaluable it can be to managing a secure network.
This is by no means an all-inclusive guide on security practices; on the contrary, it should be considered the lowest bar to aim for when implementing proper practices with IPMI. Every network is different, and as a result, every network will require different methods to administer and harden it properly. Thanks for taking this journey with us, and please don’t hesitate to reach out with questions or comments on any of our social media.
We’ve created detailed, step-by-step guides on how to do things talked about in this article such as create and change IPMI users and passwords, BMC port blocking, and updating your BMC IPMI firmware – so if you’re more interested in a No-Fuss-No-Muss-No-Filler-All-Killer, get down to business guide – check out these links:
As a 45Drives customer, you’re our top priority! So if you feel inclined, reach out to your account manager or submit a request through our website if you want us to work with you on anything discussed in this blog post today, or anything as it pertains to your 45Drives product.















